Latest Version 1.0.2
May 24, 2021
This app is archived. App archiving documentation
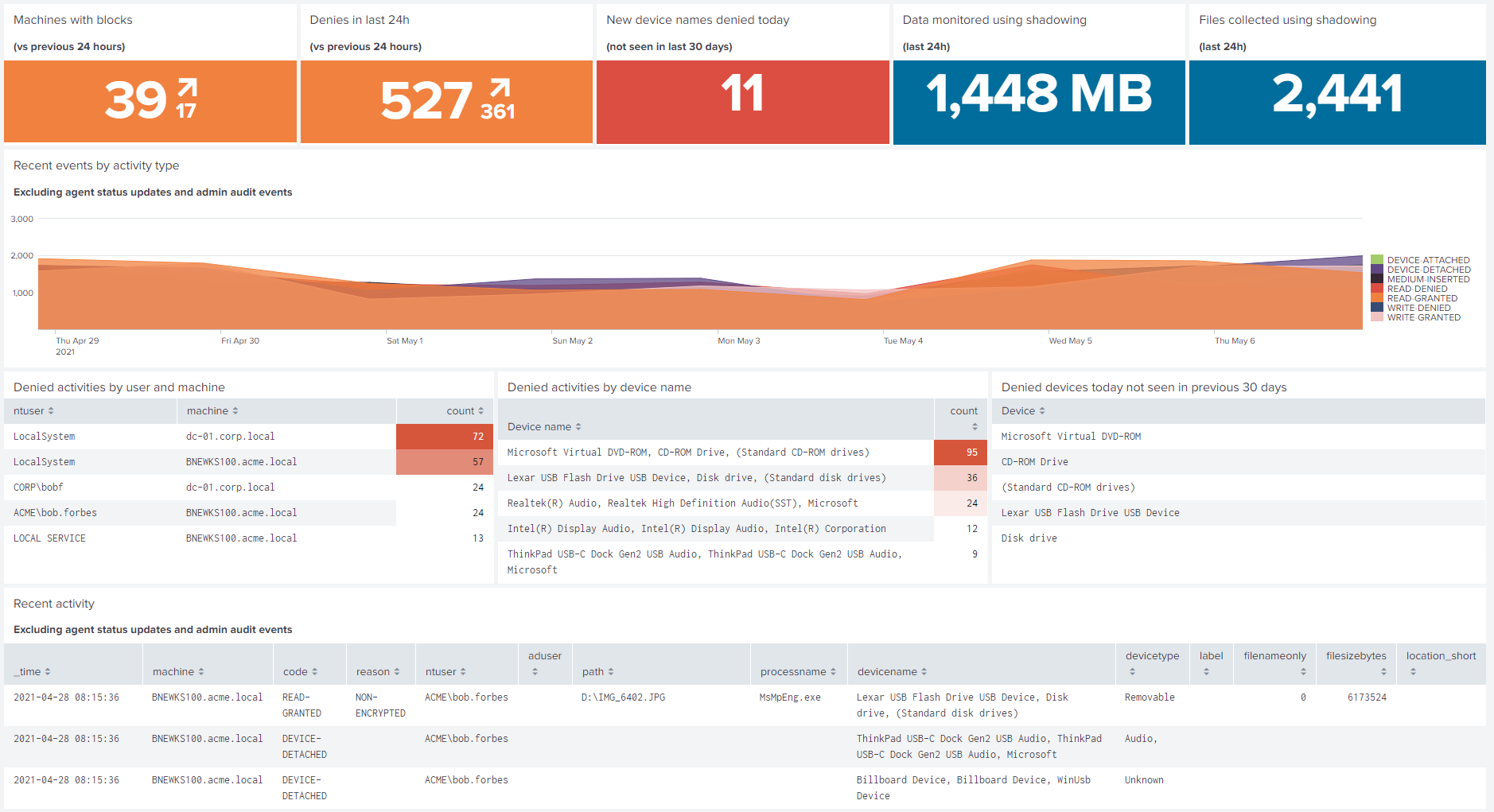
The Ivanti Device and Application Control App for Splunk provides pre-built dashboards for IDAC data that is imported with the IDAC Add-on for Splunk.
(0)
Categories
Created By
Type
Downloads
Splunk Answers
Ask a question about this app listing(Opens new window)Resources