This app is archived. App archiving documentation
Atlassian JIRA Issue Alerts add-on for Splunk
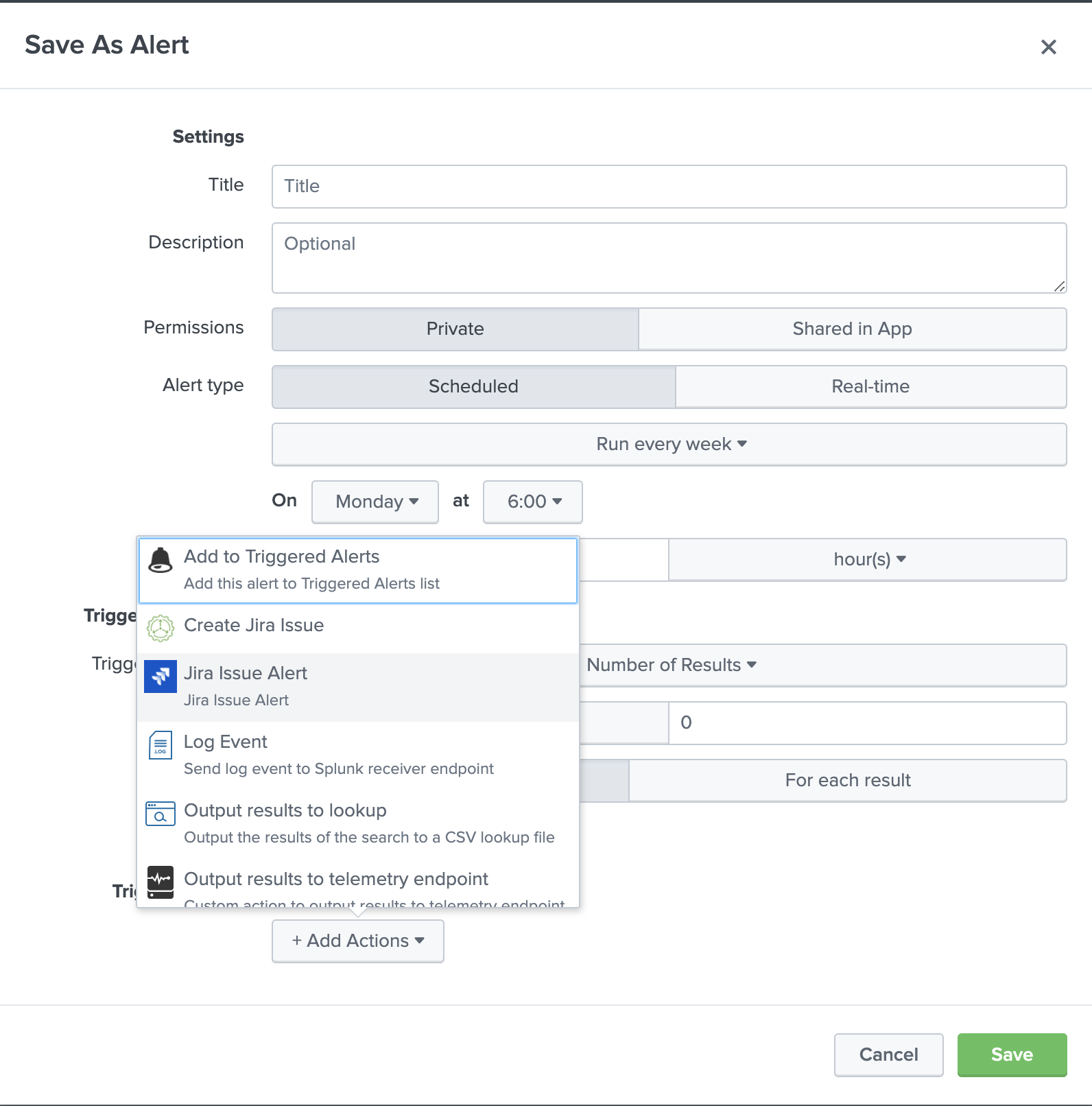
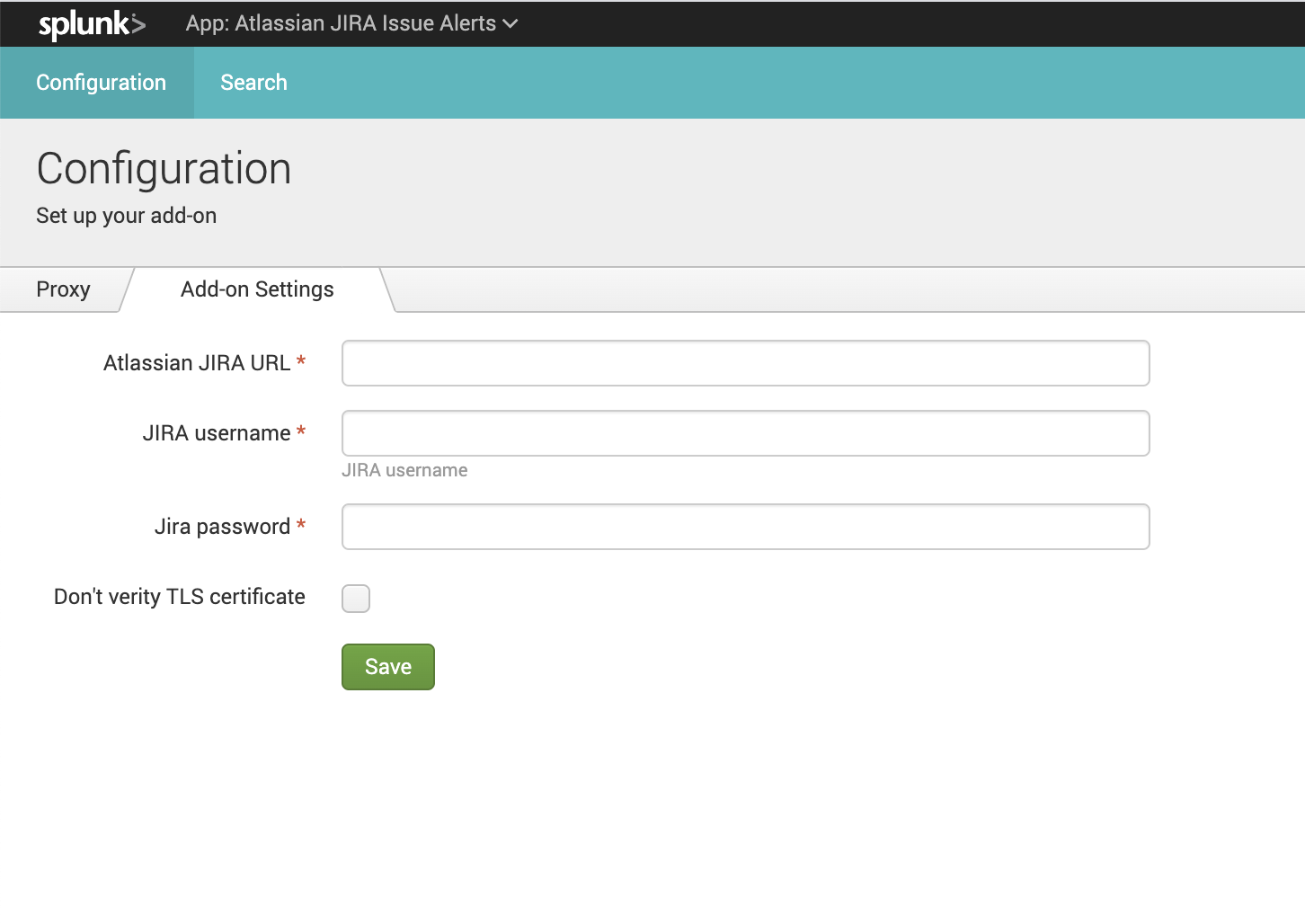
This add-on helps to create customized Jira issues based on triggered events in Splunk. It supports both Atlassian Jira Cloud and Atlassian Jira Server versions. Automatically detects which APIs need to use. Features: 1. Cover all standard necessary fields in Atlassian Jira for issue creation such as Project, Summary, Issue Type, Priority, Description, Assignee, Labels, Components. 2. Add the result of Splunk Alert into the Jira issue at the end of the description field. There are two possible views of added data 1) The table view where the table head consists of Splunk Alert result fields 2) The list view when the result of Splunk alert will be added as a Jira code snippet. 3. Possibility to use one additional custom field to create Jira issues. 4. Control what information from Splunk Alert will appear in Jira issues. Pass search result values dynamically into Jira issues. Not necessary to use a digital ID of values in the Jira field. All fields take human-readable values. Sample: you have a Jira project with the short name “CORP” with id=2331. In the configuration of Splunk Alert, you don’t need to use the Id of Jira Project. You need to use the name of Project “CORP”. Atlassian JIRA Issue Alerts add-on will automatically convert human-readable values into digital Id. 5. Possibility to assign issues to specific people even if you don’t know UUID in Jira Cloud. Assignment by username.


4
(4)
Categories
Created By
Type
Downloads
Splunk Answers
Ask a question about this app listing(Opens new window)Resources