Latest Version 1.4.0
January 17, 2022
This app is archived. App archiving documentation
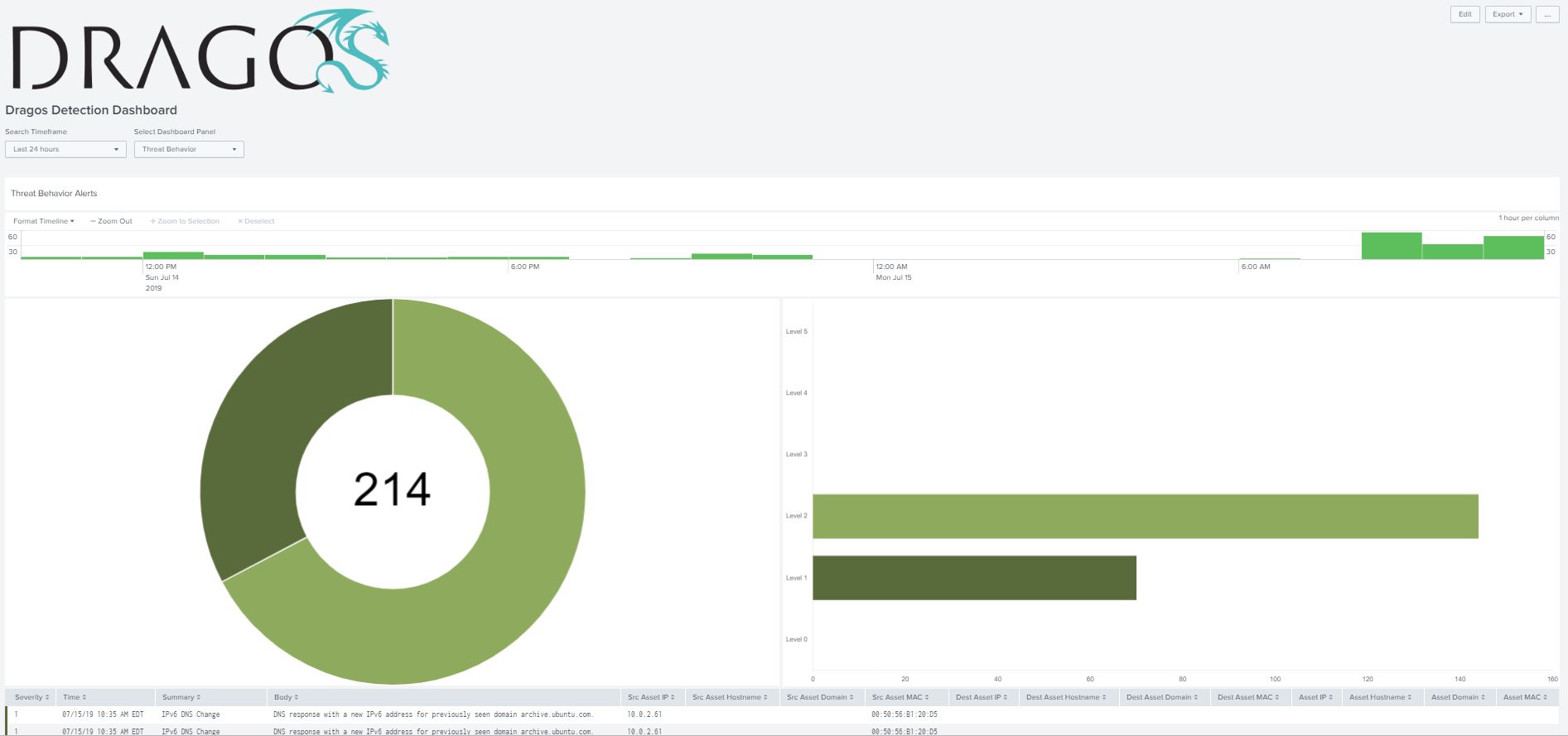
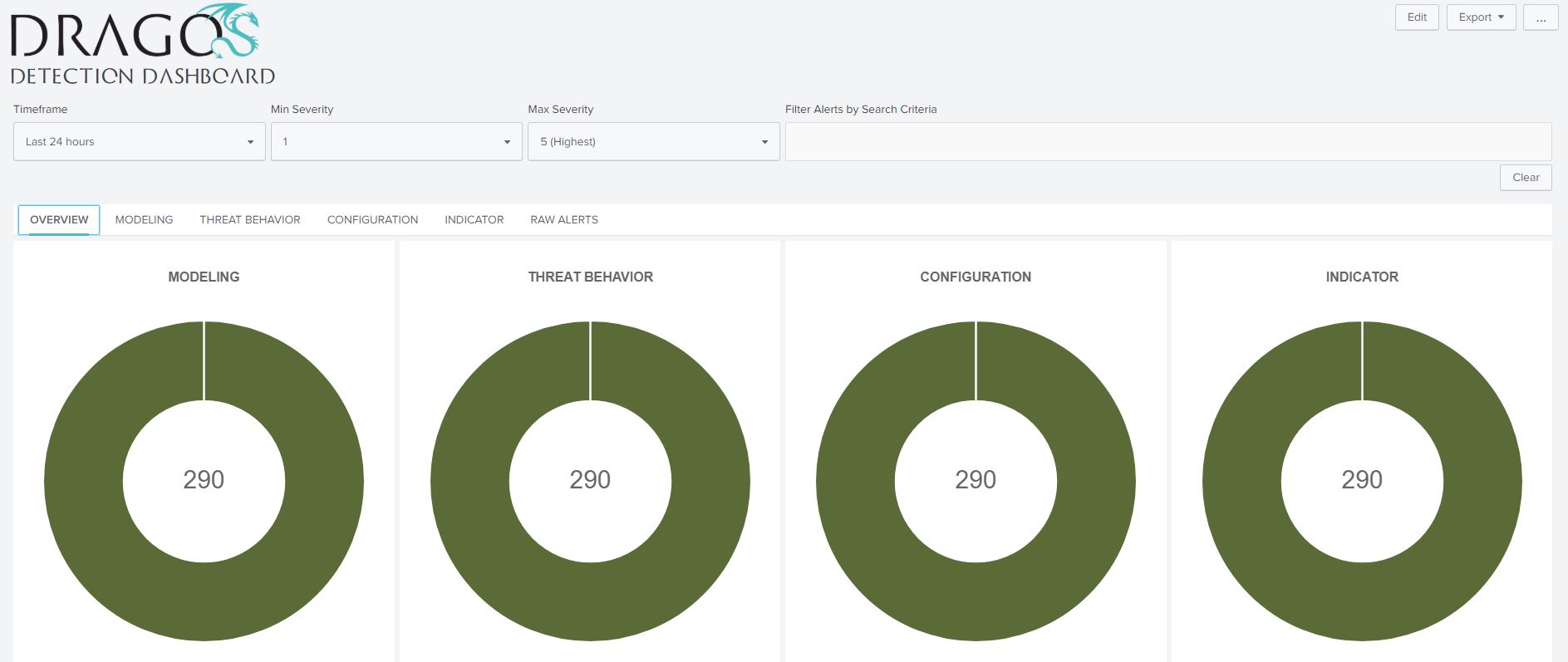
The Dragos ICS Threat Detection App for Splunk empowers users with the power of the Dragos Platform for ICS/OT asset visibility and threat detection to provide a unified view of threats and events across the converged IT and industrial OT environment. The four detection quadrants and alert severities in the Dragos Platform are presented in the Splunk App delivering a familiar and consistent user experience.
(3)
Categories
Created By
Type
Downloads
Splunk Answers
Ask a question about this app listing(Opens new window)Resources