Latest Version 0.1.1
March 7, 2016
This app is archived. App archiving documentation
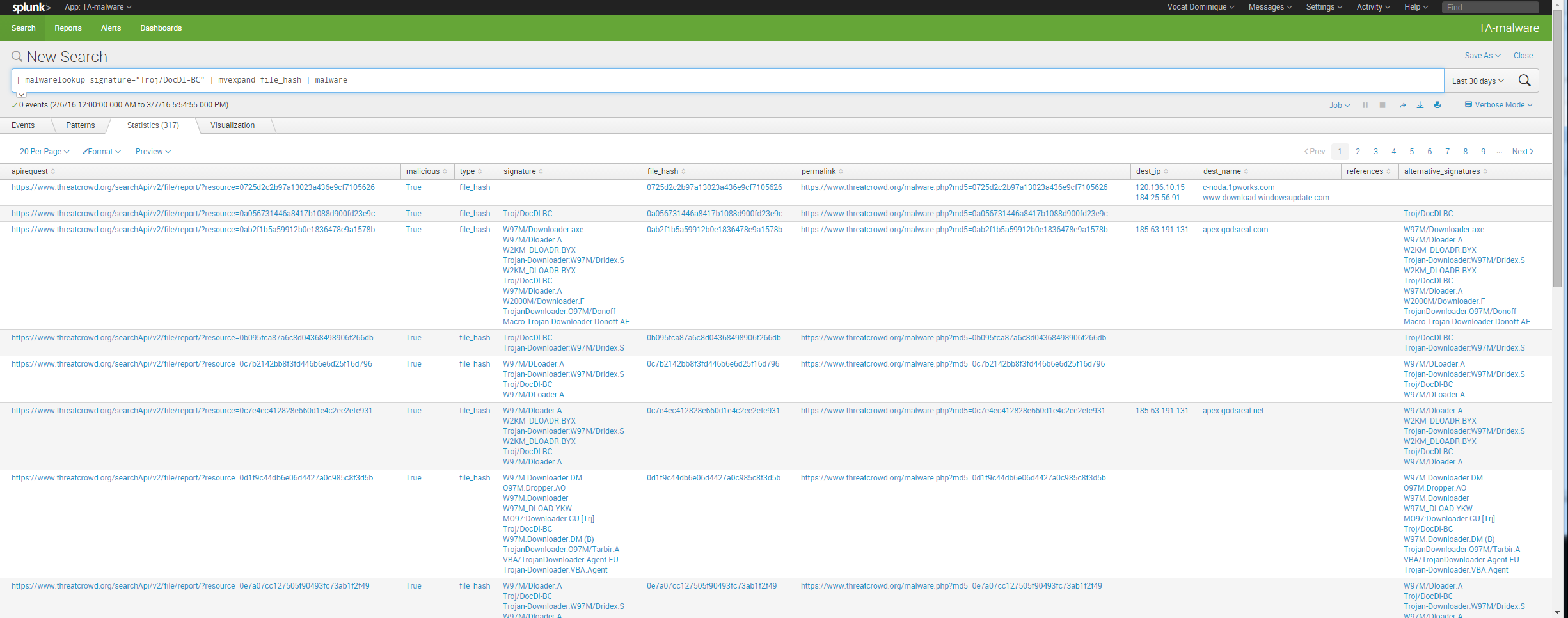
Enrich your logs containing md5 hashes or torjan names with data from internet services notably threatcrowd.org (excellent service).
(1)
Categories
Created By
Type
Downloads
Splunk Answers
Ask a question about this app listing(Opens new window)Resources