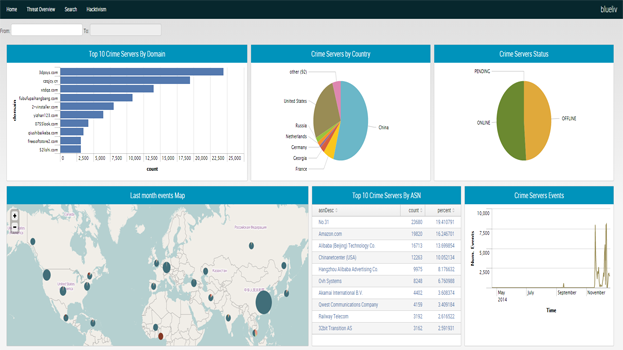
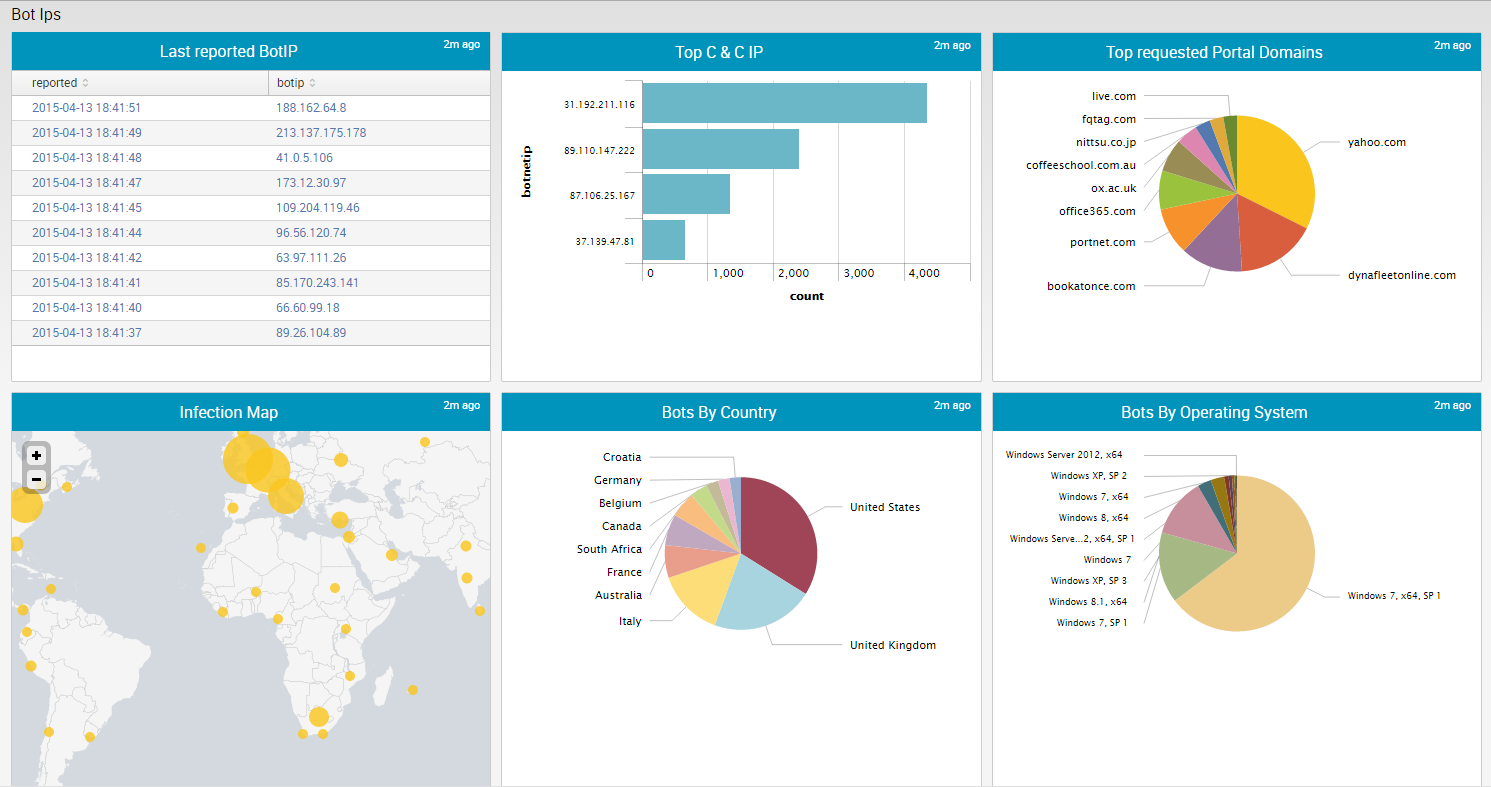
Splunk App for Blueliv automatically integrates Blueliv's Cyber Threat Intelligence into Splunk.
The use of this app will add Cyber Threat Intelligence to your existing data, addressing a comprehensive range of cyber threats including compromised URLs, domains, IPs, etc. to turn global threat data into predictive, actionable intelligence specifically for your enterprise and the unique threats it faces.
Our powerful networks of specialized search engines constantly scour the web for up-to-the-minute data and delivers real-time actionable information
Unsurpassed cyber threat intelligence, now at your disposal.
Categories
Security, Fraud & Compliance
Created By
Blueliv Security
Resources
Log in to report this app listing