Latest Version 2.0.0
July 5, 2017
This app is archived. App archiving documentation
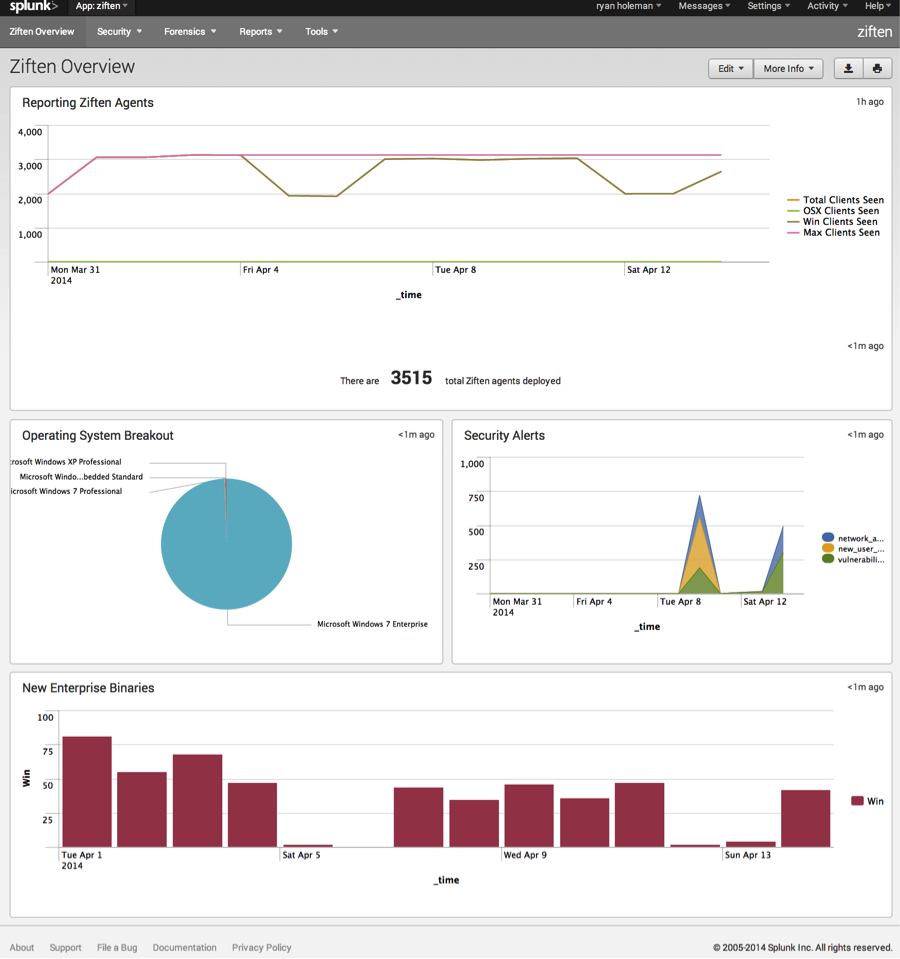
The Ziften Zenith App provides continuous monitoring and detection & response of enterprise endpoints to enhance security and IT device hygiene posturing. The product provides real-time, rapid detection, and actionable response to Indicators of Compromise (IOC's). The Ziften Zenith App provides native integration of comprehensive endpoint visibility into Splunk, with the ability to combine that information with threat feeds and network intelligence for an end-to-end view of IOC's. The product is delivered with a variety of out-of-the box dashboards for easy ramp-up and customization.



(7)
Categories
Created By
Type
Downloads
Splunk Answers
Ask a question about this app listing(Opens new window)Resources