Latest Version 1.2.7
November 14, 2018
This app is archived. App archiving documentation
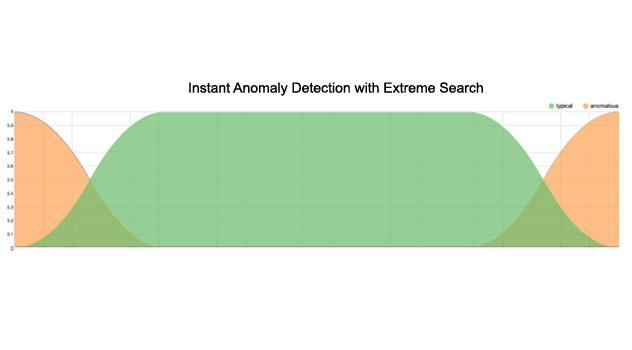
Extreme Search Visualization (XSV), is designed as a "helper" app for Scianta Analytics' Extreme Search for Splunk. Co-developed by Scianta Analytics and Splunk Inc., Extreme Search (XS) is now part of the Splunk App for Enterprise Security (ES). XSV provides a robust set of tools to help you create, manage and explore Extreme Search knowledge objects. Additionally, XSV provides valuable documentation about Extreme Search beyond what is included in the app.



(4)
Categories
Created By
Type
Downloads
Splunk Answers
Ask a question about this app listing(Opens new window)Resources